Security Considerations for the IIoT Challenge
Industrial operators are increasingly implementing IP or IIoT connectivity, enabling more capabilities at the edge of their networks and opening the door to more new applications and analytics.
April 2, 2016

By Glenn Longley
For decades, Supervisory Control and Data Acquisition (SCADA) systems have played a significant role in industrial operations. Industries like oil and gas, electric power, agriculture, and utilities have implemented SCADA systems and networks to collect data and automate processes — and they’re always looking to automation systems for more effective ways to operate.
The ability to collect more data from geographically dispersed field assets in remote locations has driven the need for enhanced communication technologies. With the emergence of continuously improving wireless machine-to-machine (M2M) technologies, networks have more access points than ever before. The number of sensors and data points collected will continue to rise dramatically with improved connectivity. This collected data helps operators improve operational decisions, save manpower and, in many instances, keep employees safe by avoiding dangerous environments.
Today, industrial network operators are increasingly implementing end-to-end Internet Protocol (IP) connectivity or the Internet of Things (IoT), enabling more capabilities at the edge of these networks. This does not make SCADA systems obsolete by any means; it opens the door to greater possibilities of enabling new applications and analytics with every single data point being captured in the system.
There are many implications for the concept of a completely connected enterprise in terms of network security. Critical infrastructure projects are only as reliable and secure as the technology serving them. Security, therefore, will ultimately be the limiting factor on how much IoT technology is deployed. With security, the traditional trade-off is either “easy to use” or “secure”— but not both. We often consider a third tradeoff, as well, features; in most cases, operators are not willing to trade off features, but it is certainly part of the equation. An operator striving for an Industrial IoT (IIoT) network must look at SCADA security, the convergence of Operations Technology (OT) and Information Technology (IT), and make a thorough assessment of what will allow them to achieve a secure data communications network and where they want to be in this triangle.
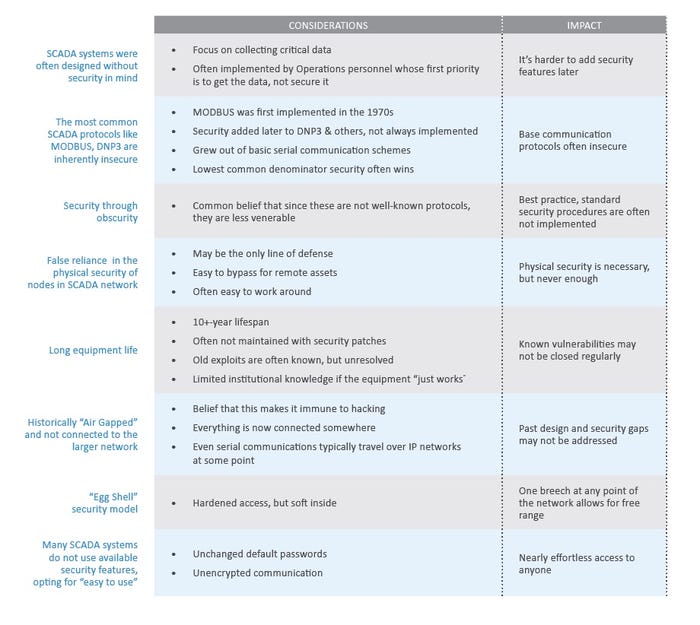
Today’s Security Challenges
Traditional SCADA systems have several challenges when it comes to security. With more data being transported than ever before, it’s important not only to secure assets, but to secure the communication link itself. Traditionally, SCADA systems have been on the outside of a firewall from the corporate IT network. Newer SCADA systems that use Ethernet devices are more security-focused with measures such as VPN, secure sockets, encryption and dedicated log-ins on the devices.
IT/OT Convergence
Traditionally, companies have a corporate firewall that divides the corporate IT space from OT space. With an IoT network, there is a need to protect the sensors and new applications on the OT side. However, if the individual devices that are connected on the OT side become compromised and the threat has access to that communication link, a hacker can push malicious data, cause denial of service (DoS), or introduce malware or viruses to the entire network — even if there is a secure communication link. There are many ways to run into problems on the IoT front if companies are not careful in their network design security implementation.
On the IT side, corporate network security typically sees many threats. Those threats require significant attention and, consequently, IT organizations have numerous options and tools to use, such as intrusion detection, log monitoring, network behavior monitoring, network inspections, whitelisting, firewalls, and more. The IT space has a much different attack surface than OT because with an IT network, the company can physically secure the building and control where the data goes in and out. Data escaping the building is relatively small in comparison to the OT space. Wi-Fi that leaks outside the building could be a vulnerability, but there are tools and ways to lock down that type of threat, and checkpoints where the IT department can analyze the traffic going through the network. In IT, bandwidth is plentiful and the network overhead associated with security is generally not a major factor.
IIoT networks, on the other hand, can span many miles with potentially hundreds of thousands of data points. An IIoT network likely consists of small embedded devices with long lifespans, making it very efficient. However, they are generally not like the Windows operating system, which is consistently conducting massive updates. Some embedded technologies don’t allow any updates, making it essential to carefully select the best devices for a network. Having thousands of these edge devices is where organizations will begin to see IT/OT convergence — many more points in the field where threats could be coming into the IT network.
Industrial organizations today are creating a connected infrastructure with IP-enabled sensors or IP/IIoT-enabled Access Gateways. The data generated by sensors at an asset location can be valuable to more than just the central control system. This might mean M2M communication with sensors talking directly to each other. It might mean that multiple systems consume the live, real-time sensor data directly from the field. It might even mean that operators connect their sensors directly to the cloud or other back office systems. If there is a way to share critical data while addressing security issues that can help provide information to key data users, then that information becomes increasingly valuable.
IIoT solutions often utilize the widely deployed security technologies from the Internet to avoid the custom, one-off solutions of past industrial security — when it was used at all. IP technology makes it easier to deploy and talk to sensors, but it also makes it easier for intruders to see and snoop on valuable data streams. Security through obscurity is not a solution. There are many common attack vectors for industrial devices that become even more relevant when considering the IIoT infrastructures and fully networked, geographically dispersed projects.
How to Select Secure Technology for IIoT
The concept of IoT offers many advantages from a business standpoint, but also opens the door to many security questions. Companies moving to IIoT need to ask these important questions before selecting a technology:
What are my requirements? Must haves vs. Nice to haves?
Are there any regulatory considerations?
What is the M2M communications technology controlling or automating? Is it essential that it operates without failure?
What data is being collected and/or transmitted with this technology? Is it time sensitive and/or mission critical?
What technology solutions have a proven track record for the applications being served?
What external factors might affect the reliable transmission and receipt of critical data from one point to another?
How does this M2M communications technology address challenges such as data encryption, network access control and signal interference?
Can the vendor describe the security mechanisms? Can I understand them?
Will this be secure even if everyone knows the security measures? (The right answer is yes, and if it’s not, keep looking)
Do we need this technology solution to be fail-safe in order to prevent or eliminate catastrophic damage from occurring?
What are the threat vectors I’m most concerned about?
Is cyber security or physical security a greater concern for this deployment?
What vulnerabilities have the Information Security community identified in the type or category of IIoT equipment I use?
What is the right tradeoff between features, ease of use and security for my installation?
Do I have a testing or evaluation plan in place?
And what ongoing improvements do I expect?
In smart grid projects, for example, operators must also take into consideration the cybersecurity reliability standards that FERC oversees. This helps operators choose a more cyber-hardened technology. On the other hand, for industries that do not have these standards, there remains a tradeoff between secure and easy to use. When strong cybersecurity has not been mandated, people tend to avoid the “harder to use” option that is typically more secure.
Conclusion
Each company is different in how it handles the influx of IoT and the resulting IT/ OT convergence. With this convergence of IT and OT, that firewall that separates the two becomes more complicated and less well defined. Traditionally, each was a separate entity; however, with IP-enabled devices, that dividing line becomes less clear. IT and OT professionals themselves might put a different emphasis on security. The IT organization is typically owned by the CIO, who is being measured on how secure they keep the network.
On the other hand, it’s less clear who is in charge of the OT. It might be a foreman, who is more concerned with the system functioning because they are being measured on system performance only. As IoT emerges, it will be increasingly important for both sides of these two worlds to focus on the same security goals without making the networks and systems so difficult to use that it interferes with the functionality.
There are many benefits to the concept of a completely connected IoT system, but this also implies more crossover between IT and OT systems. Companies need to prioritize security in their quest to create end points for all their field assets. Some industries, like the smart grid, are already experiencing mandates that ensure a more cyber-secure network. With others, however, it is still up to the organization to make security a top priority. There are technology providers available that are security focused and will provide those extra layers of security to the OT network.
Article was originally published on IndustryWeek.
You May Also Like





