IoT device security: A comprehensive look, from edge to cloud
Cybercriminals have an array of potential attack vectors to choose from when targeting IoT implementations. Here’s how to work towards comprehensive security in Internet of Things applications.
September 23, 2017

By Mohit Bhardwaj
The Internet of Things may have a significant economic potential, but it also gives malicious actors an ever-expanding toolbox for cyberattacks. Gartner estimates that 5.5 million “things” get connected each day. It’s no wonder that hackers are beginning to target IoT devices with weak security for botnets and other attacks: they are often low-hanging fruit.
As both physical and digital threats increase, the need to find technologies to reduce such risks is also rising. This article will discuss the vulnerable points in an IoT application and the key strategies to resolve them, including details on maintaining supply chain integrity. It will also cover the fundamental elements needed to create a robust security paradigm.
Potential attacks for IoT applications
A handful of IoT-related attacks seem to receive the most attention in the popular press. There is, of course, the Mirai botnet that brought down a chunk of the internet last year. There’s BrickerBot, which renders insecure IoT devices unusable. On the industrial side, Stuxnet is famous for causing physical damage to nuclear centrifuges in Iran. And then there is BlackEnergy — a malware variant that shut down a portion of Ukraine’s power grid.
Attacks with a physical component: IoT attacks at the physical layer of the OSI Model require unauthorized access to physical sensing, actuation and control systems. Consider how electronic car theft works as an example. Since cars are essentially computers on wheels, hackers have a variety of options at their disposal. They can clone the radio signals from a key fob to open a locked vehicle. A hacker with physical access to a vehicle’s Controller Area Network (CAN) bus underneath the steering wheel can cause all sorts of mischief: They can unlock the car’s immobilizer that stops a thief from driving away and reprogram a new key for the vehicle. Access to the CAN bus could also enable them to hack the speedometer, door locks and other components.
The similar threat applies to industrial control systems, which have a decades-long history. Many industrial machines make use of supervisory control and data acquisition (SCADA), a technology that was created decades ago without much thought about security. As a result, an attacker with physical access to a SCADA system can cause significant damage to industrial facilities and critical infrastructure.
Similar threats could apply to medical devices. An attacker could gain access to an implantable device such as a cardioverter defibrillator or an external medical device such as an insulin pump to install malware.
Pure software attacks: This category includes malware variants such as viruses and trojans and worms. Also in this category is fuzzing, in which random data is thrown at software to see how it reacts. Distributed Denial of Service (DDoS) attacks can be software-based as well, although they can also occur at lower levels of the OSI Model. One potential example of an IoT-related DDoS risk would be safety-critical information such as warnings of a broken gas line that can go unnoticed through a DDoS attack of IoT sensor networks.
Network attacks: One of the biggest vulnerabilities of IoT devices is their wireless connectivity, which can make them remotely exploitable. Here, there are a variety of possible attacks that are possible on the devices, or “nodes,” connected to the network.
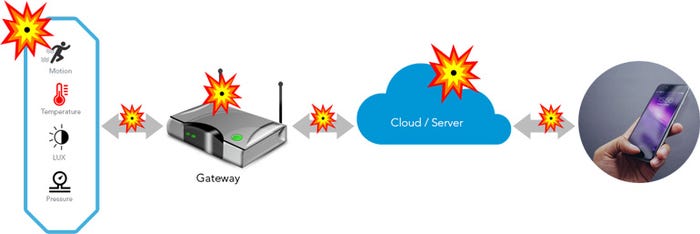
In an enterprise Internet of Things context, those nodes typically communicate with the gateway that is the core of that implementation. The node connects all of the IoT devices to the cloud.
Let’s assume that we have an industrial IoT application with interconnected gateways linked to each other in a mesh network. If a hacker jams the functionality of a gateway with denial of service requests, they can bring down the whole IoT project. Thus, a single attacker can stop the IT and OT elements of a system from interacting, as we discussed in the article “IoT gateway architecture: Clustering ensures reliability.”
Cryptanalysis attack: In this type of exploit, a hacker tries to recover an encrypted message without access to an encryption key. Examples include brute-force attacks when a hacker tries every possible password combination to gain access to a system. The known-plaintext attack, with roots stretching back to WWII, is another example, in which a hacker has access to unencrypted text as well as its encrypted counterpart. Another possible exploit in this category is a so-called “man-in-the-middle-attack” where hackers position themselves in between two network nodes to gain access to the communication between them.
Side-channel attack: A side-channel attack is the IT equivalent to spotting a liar by their nervous behavior while fibbing rather than what they say. In other words, the attacker can infer which encryption is used without having access to either plain or ciphertext. There are myriad ways this might work. An attacker might study a device’s power use or optical or radio emanations. A hacker could even observe the sounds coming from the electronic components within a device and use that information to crack its encryption key.
Side-channel attacks are a threat to IoT devices as well as traditional IT infrastructure. There is, however, a big difference between IT and IoT security. IoT systems typically use weaker authentications and have less-effective layers of security than conventional IT infrastructure.
Why it’s time to batten down the IoT hatches
After hearing countless predictions about billions of connected devices and trillions in market value, it’s easy to understand why Internet of Things devices are proliferating. But the landscape certainly poses a challenge to cybersecurity professionals. Many of the IoT devices out in the field now have poor security. The complexity of the IoT landscape makes it hard to tick all of the security boxes.
In theory, it should be relatively straightforward to answer questions like these: Is the cloud architecture of your IoT application configured correctly? How many IoT devices are on your network? Are any of them are using hard-coded passwords? How would you react if your IoT implementation was hacked?
Security problems that can besiege IoT applications include:
Lack of mature technologies and business processes: There is a proliferation of diverse standards. This complexity can, in turn, help enable the introduction of vulnerabilities and provides attackers with a way to infiltrate the enterprise.
Limited guidance for lifecycle maintenance and management of IoT devices
Physical security concerns
Lack of agreement on how to approach authentication and authorization for IoT edge devices
Lack of best practices for IoT-based incident response activities
Audit and logging standards are not defined for IoT components
Supply chain vulnerabilities
Enterprises with IoT applications can achieve trustworthiness at each level of the supply chain, including people, process, design, manufacturing and delivery levels. If there is a lack of information transfer at any link in the supply chain, it can enable security vulnerabilities and possibly open it up to a breach. Enterprise companies should have a policy in place to prevent unauthorized access to important systems while weeding out rogue vendors who could leverage technical loopholes to obtain sensitive data.
How to enable security from edge to the cloud
Maintain supply chain integrity: Enterprise companies need to ensure that their vendors and suppliers have defined Supply Chain Management (SCM) procedures that include baseline testing of components and specifications for parts used in IoT projects. In addition, they should be able to provide information on the entire manufacturing process. They should also share any changes in the system or any technical vulnerabilities in components with the IoT system owner. Any updates of the system such as changes in configuration, software changes and so forth should also be shared with the system owner or operator. Supply chain management systems should be able to consult a dashboard where they can easily access vendors’ and suppliers’ details, and any changes in the specifications of the components or parts.
Establish a chain of trust: Ensuring a high degree of security for an IoT implementation requires that devices, gateways and applications that are part of an IoT value chain. A trustworthy system enables the “chain of trust,” and this level of confidence should be maintained in the entire lifecycle of the system and adapt to new changes.
The basic categories for building a chain of trust, according to the Industrial Internet Consortium’s security framework include:
Security, which is the assurance of a system that it will remain secure from any outside threats, and attempts to harm the system. It also includes confidentiality of the information that it will not be disclosed to any unauthorized entity, the integrity of the system to avoid inappropriate changes and destruction of the information, and availability of the system to provide instantaneous information to an authorized user.
Safety, which is the condition at which a system runs without posing a threat of danger includes safeguarding people and physical OT assets.
Reliability is the ability of a system or component to perform its required functions under stated conditions for a specified time. Reliability and availability are correlated. Reliability can be thought of like a fraction: it is the amount of actual availability over scheduled availability, as affected by things like scheduled maintenance, updates, repairs and backups. Hence, when the scheduling is done properly, it is possible to get the actual availability (reliability) closer/equal to the scheduled availability.
Resilience is achieved by designing the system so that, when a failure occurs, the system can find an alternative way to accomplish the task. Failure in a single component should not affect other parts of the system. The system should be able to deal with failed or faulty processes automatically.
Privacy is the ability of personnel or an organization to have control of the information flow. It includes matters such as the confidentiality of processing and transferring data and who has access to that data.
When a system has all of these characteristics, it should be able to stand up to risks predicted for the system.
Communication and network security
An important aspect of any connected device or IoT system involves peer-to-peer communication between gateways and devices as well as communication to the cloud.
The following are critical from a security perspective.
Channel-based communication using sub-channels such as data channel, control channel, management channel can enable secure communication. For example, security policy management and event monitoring messages need to be segregated at each level of communication.
State-based management of a system is the most prominent way to secure the system. State analysis enables the ability of a system to react to unauthorized access requests.
Categorization of unauthorized and authorized devices and applications that are engaged with the system.
Geo-fencing of devices for unauthorized movement analysis.
When a gateway receives a flood of messages, it can be overwhelmed in one form of a “distributed denial of services” or DDoS attack. Anti-jamming technology can be used to address certain forms of these attacks.
Data security
Securing data at endpoints involves data-at-rest (DAR) and data-in-use (DIU). The communication security is required for data-in-motion (DIM). For DAR, TPM (Trusted Platform Module) storage key can be used to secure the data. For DIU, runtime integrity techniques can be used to monitor memory access, and detect & protect against memory attacks. For DIM, data tokenization (a type of cryptography) can be used to protect sensitive data with encryption that can be decoded by authorized parties. See the example below showing a hospital’s patients database:

(Image Source: [1], Industrial Internet of Things Volume G4)
There are three main techniques for cryptography: shared key, certificate-based authentication, and token-based authentication.
Cyber theft prevention
From a theft perspective, the most common type of targets are IP addresses, Fully Qualified Domain Names (FQDNs), and malicious URLs. There are many frameworks that can identify the cyber threats and mitigate them, including the Collective Intelligence Framework (CIF),
Trusted Automated eXchange of Indicator Information (TAXII) and Structured Threat Information Expression (STIX). Such technological frameworks continuously analyzes data, creating a chain of messages. In the STIX framework, for instance, whenever a user asks for specific data, the system provides information on cyber risks, threat actors, a recommended course of action and other information. For building a chain of trust, it is important for IoT devices to share threats and other pertinent information with the nearby devices that are on the same network.
Hardware security
Hardware security can be achieved in an IoT solution with Trusted Platform Modules (TPMs) and Trusted Execution Environment (TEE). TPM is essentially a chip that is installed on an IoT device near the CPU. It is used for mainly cryptographic operations, which creates a security key, saves it, stores the data and other related operations. They can use to ensure the integrity of a platform, for disk encryption and password protection.
TEE is a separate execution platform that differentiates the operational capability from the security functionality. It consists of APIs, kernel and a trusted OS that runs security checks, parallel to the standard OS. TEE consists root of trust (RoT), which includes a trusted boot platform, a measured boot process and an attestation process. TEEs also help ensure the integrity of applications and data storage. A trusted boot platform enables a secure boot, avoiding problems with malware that self-installs during the boot process. A measured boot process provides data on every process of the boot sequence before executing it on the standard OS. The attestation process allows the process to share its trustworthiness and security parameters with other trusted sources, securely. TEEs also help ensure the integrity of applications and data storage.
Blockchain-based security
While blockchain is best known for its use in cryptocurrencies like Bitcoin, the technology can be used for authentication in IoT networks as it uses a “micro-ledger” as evidence for peer-to-peer communications. Blockchain can record the communication history of two IoT gateways or devices. Once an action (or “transaction”) get stored in a micro-ledger, then it cannot be altered in the future. While certificate-based encryption technologies can be forged, Blockchain has the advantage of being distributed, and thus supports the security concept of non-repudiation, meaning a person who triggers an action on an IoT network cannot deny doing so.
Conclusion
IoT security has emerged as a critical issue for connected technologies at large. There is a multitude of security threats targeting enterprise and industrial companies. Organizations with IoT initiatives shouldn’t assume that, just because they haven’t been hacked yet, that they never will be. Hackers can strike at any time. Without a robust and properly designed security structure that extends to IoT deployments, cybercriminals can do considerable damage to your company’s assets and reputation.
You May Also Like






