Data diodes only allow data to flow in one direction, effectively shielding the sending devices from an outside attack.
September 27, 2021
By Rich Castagna
Like stern traffic cops, data diodes reinforce a one-way route for data traveling through a network, ensuring that the IoT devices behind the diodes won’t be compromised by malicious incoming traffic.
Simple but elegant solutions, data diodes provide hardware-based security to Internet of Things (IoT) environments. These environments have become more vulnerable, as the volume of connected devices grows, and the networks stretch to wider and more remote geographies. For any administrator of an IoT infrastructure, security is the foremost concern today—with good reason.
“IoT devices now make up 32.72% of the infected devices observed,” Nokia noted in its “Threat Intelligence Report 2020,” which chronicles malware activity in networks based on data collected by the company’s security software. “Compared with 2019, the share occupied by IoT devices in the overall device breakdown has increased by 100%, from a previous share of 16.17%.” The threat to IoT endpoints is so severe that Nokia concluded, “Cybercriminals are focusing their effort on IoT and mobile devices.”
“The growing digitalization of critical infrastructure with an increasing number of IoT devices is raising the bar for network security,” wrote Andres Guilarte, global product manager, connectivity and IoT for Siemens Mobility in a response to emailed questions from IoT World Today.
How Data Diodes Protect Networks
A diode is “a device, as a two-element electron tube or a semiconductor, through which current can pass freely in only one direction,” according to Dictionary.com.
Data diodes apply this technology to network infrastructure to allow data to flow in one direction and to stop data from traveling in the other dead in its tracks. And while they have grown in sophistication and capabilities since their introduction several decades ago, data diodes are still essentially single-purpose devices that provide a relatively straightforward service.
Data diodes work similarly to other hardware-based network flow controllers. For example, a similar effect has been achieved by altering cable connections, such as removing pins from an RS-232 connector to prevent data flow in one direction. That’s a brute-force solution, to be sure, and one that lacks diode capabilities like protocol awareness which can be critical to network operations.
There are also network gateways that can limit or eliminate certain data streams through a network, but they tend to have similar complexities, hardware requirements and updating issues to firewall technologies. “One of the benefits of diodes is that you don’t need to patch them,” said Johan Vermij, Research Analyst for IoT at 451 Research, “so they’re better suited than firewalls for sites that are far away.”
“It’s a hardware physics based one-way transfer,” said Brian Romansky, chief innovation officer for diode manufacturer Owl Cyber Defense. “You can’t secretly or accidentally have a backwards port open that you forgot about.”
According to Romansky, data diodes date back to the cold war era. “The data diode concept came out of some work that was actually a Department of Defense program and actually ties back to a time when the US and Russia had signed a nuclear decommissioning deal,” he noted. The two parties needed to share data to ensure compliance with the pact. “How do I share data with my most untrusted enemy from my most secretive data set? And how do I make that connection work without being a very manual, tedious process? And so the data diode was invented as a way to do that.”
Given their defense and intelligence pedigree, it’s not surprising that data diodes show up in a Department of Homeland Security recommendation. “If one-way communication can accomplish a task, use optical separation (“data diode”),” the department suggests in its “Seven Strategies to Defend ICSs” publication.
Where Data Diodes Fit in a Security Scenario
A successful IoT security strategy will likely require a multilayered approach using software and hardware security products. A typical IoT environment comprises smart and not-so-smart devices to collect and analyze data. The smart devices might have more inherent vulnerabilities, but they also have the compute power to run sophisticated security software. The less intelligent endpoint devices rarely have the processing power to do anything other than their assigned tasks.
Encryption and firewalls are standard fare in IoT security scenarios, but they, too, may fall short in certain areas, leaving potentially vulnerable gaps. The more data traffic that’s encrypted the better, but encrypting and decrypting data can introduce latency into the network and cause problems for systems that need to respond in real-time to data from sensors and other endpoint gear.
Firewalls, a staple of IT network security, also figure prominently in the discussion. Firewalls can effectively prevent incursions and control the flow and direction of data movements in the network. The downside to firewalls are that they require dedicated servers and need to managed and monitored, and frequently patched and updated. That can become a burdensome chore for complex networks that require multiple firewalls running simultaneously.
“Considering the ever-increasing connectivity and rapidly increasing cyberattacks, firewalls are no longer the only go-to cybersecurity option,” noted Siemens’ Guilarte.
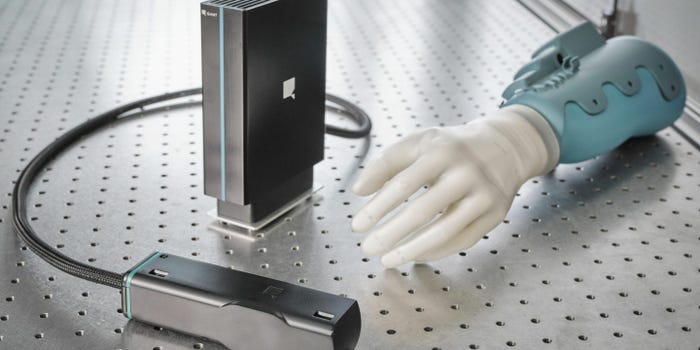
A burgeoning IoT security technology field involves the use of hardware-based security devices. Sometimes referred to as hardware secure modules—or HSMs—this category includes both security-specific devices like data diodes as well as endpoint devices that have been enhanced with chips that provide security features.
Key Facts About Data Diodes
While data diodes have found their way into a variety of environments and operations, their most often cited implementation is to isolate reporting from data collection. “The most common use case that we see is historically been actually data historian replication,” Romansky said. “You can get reports and information out of that system while guaranteeing that no threats can come in.”
Today, however, diodes are used in many more ways to enhance IoT security. Some of the critical applications that diodes can help safeguard include the following:
Backup and disaster recovery repositories
Replication of database and other application data
Traffic flowing to/from remote sensors and other facilities
One concern that potential implementers might have is the ability for receiving devices to acknowledge that data has been received.
“One-way data transmission is basically a blind transmission if the sending network cannot verify the receipt of the data from the other network,” noted 451’s Vermij. Without that, sending systems can’t confirm their data was received. “That could result in retransmission which would use up additional bandwidth.” Vermij added.
But modern data diodes are much smarter than the simple one-way switches they once were. With a built-in understanding of certain communications protocols, diodes can provide the necessary acknowledgement without exposing the data.
“Anytime you try to establish a TCP session, you require an acknowledgment to come back–it’s session based,” said Romansky. He noted that Owl’s diodes have built-on proxy servers to address the acknowledgment issue. “When you make a connection to a data diode, you’re actually connecting to an application that’s running on the diode and you’re connecting to an application that we’ve developed that is aware of the protocol that you’re trying to send out.”
Another consideration might be how data diodes will work in the context of existing security systems, primarily, how will the security systems be able to monitor the devices that are behind the data diodes. Proper placement of the data diodes will ensure that the security apps get what they need. “You can pass that monitoring data through the diode and deliver it to if you have a SOC or a NOC where you’re collecting analytics,” said Romansky.
Siemens’ Guilarte noted that a data diode isn’t likely to interfere with existing security systems, but it may even make them better. “It is not vulnerable to software changes or mismanagement,” wrote Guilarte, “it is secure by default, and no misconfiguration or software vulnerability can make it insecure.”
Data Diodes Buyer’s Checklist
Data diodes typically cost a few thousand dollars, with the price rising as more sophisticated features are added. That’s right in line with the cost of a firewall, but the useful lifetime of a diode far outstrips other network products.
“Some have been running for 20 years without maintenance,” noted Vermij.
Guilarte noted that this reliability might be a deal-beaker for some IoT environments. “Given that data diodes are used in highly secure/sensitive systems, long-life cycle support is a must in order to match the long-life life cycles of such systems,” he wrote.
Some other features to be aware of when shopping for data diodes include throughput capabilities and protocol support, both of which will be dictated by current and planned network architectures.
Security ratings may also be a factor. Many diodes are rated using the Evaluation Assurance Level scale of EAL1 through EAL7. EAL7 is the highest rating and denotes that the product has undergone formal design verification and has been tested. Other standards may also come into play. “Independent security assessment of the development, manufacturing and support by internationally recognized standards like IEC 62443” should also be considered according to Guilarte.
The Future of Hardware-Based IoT Security
As effective as data diodes are, they may be challenged by a growing number of wide-ranging IoT networks supporting thousands or hundreds of thousands of endpoints. With that scale and network complexity, effective security will have to be more localized.
“Network security is becoming impossible, so we have to bring security to the edge, to the device itself,” said Vermij. “Complete air gapping is not really practical anymore.”
Data diode manufacturers understand that traditional diode operations may not suffice and are porting their technologies to chip-sized platforms that can be incorporated directly into endpoint devices. “Once you have the capability of doing this kind of inspection in an field-programmable gate array, you now dramatically reduce the size, weight and power and cost of a packet handling solution. So now you can start to think of where else can I put this?”
You May Also Like

.png?width=700&auto=webp&quality=80&disable=upscale)
.png?width=300&auto=webp&quality=80&disable=upscale)


.png?width=300&auto=webp&quality=80&disable=upscale)