August 9, 2018
The chief executive officer of HackerOne, maker of a quickly growing bug bounty program platform, draws inspiration from eSports
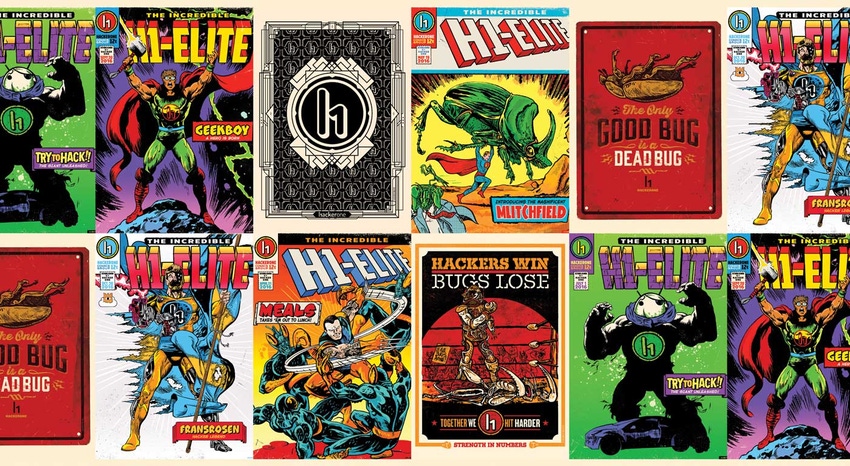
The startup HackerOne doesn’t fear hackers. It glorifies them. Elite security researchers using the firm’s bug bounty program are commemorated on comic book covers the firm commissions. The company plasters the faces of some of its most-talented hackers in its promotional materials and, earlier this year, extolled their talents in front of the U.S. Senate’s Subcommittee on Consumer Protection, Product Safety, Insurance and Data Security in a discussion.
The fundamental goal of the company is, of course, aligned with that of traditional cyber firms: They want to help their clients reduce cyber risk. But the company’s financial model stands out from many in that its clients pay for quantifiable results. If a security researcher identifies a valid security bug that its internal vulnerability response team validates, then the client pays for that disclosure. “You know it’s money well spent,” said HackerOne’s Chief Executive Officer Mårten Mickos. “It’s a bit like going to the dentist. If they don’t find anything, you’re happy. If they do find something, you are glad they found it.” If researchers find a minor or major vulnerability, the payout is proportional.

 HackerOne isn’t the only company to offer a bug bounty platform. Bugcrowd and Synack offer similar crowdsourcing-based offerings. In addition, large tech companies such as Apple, Facebook, GitHub, Google and Intel offer bug bounty programs. But HackerOne is the biggest firm of its kind and is rapidly expanding. It’s grown its head count from 60 to 140 in the past year. According to Crunchbase, the company has raised $74 million to date, after scoring $40 million in Series C funding earlier this year. “We have more money in the bank than [our competitors] have raise,” Mickos said.
HackerOne isn’t the only company to offer a bug bounty platform. Bugcrowd and Synack offer similar crowdsourcing-based offerings. In addition, large tech companies such as Apple, Facebook, GitHub, Google and Intel offer bug bounty programs. But HackerOne is the biggest firm of its kind and is rapidly expanding. It’s grown its head count from 60 to 140 in the past year. According to Crunchbase, the company has raised $74 million to date, after scoring $40 million in Series C funding earlier this year. “We have more money in the bank than [our competitors] have raise,” Mickos said.
The number of verticals the company works with is expanding from an initial focus on consumer-facing companies to include health care clients, automotive firms and government agencies such as the European Commission, the U.S. General Services Administration and the U.S. Department of Defense. Internet of Things applications are a growing focus, but Mickos also stresses that many IoT devices are equipped or attached to user interfaces on mobile apps, websites or internal networks. “IoT security is not just a matter of securing the device. It’s also a matter of securing the software that operates on the device,” Mickos said. “We will not stop at anything. We do Web, IoT, mobile, API, on-prem software and CPUs.”
As organizations continue to deploy more connected devices and the level of cyber awareness steadily increases, so does the volume of cybersecurity products, vendors and noise. While time-worn defense such as firewalls, encryption, threat detection software and so forth are all essential, a cybersecurity strategy based solely around discrete cyber products can offer unclear benefits.
 As of May 2018, cybersecurity professionals using the HackerOne platform have identified 72,000 vulnerabilities.
As of May 2018, cybersecurity professionals using the HackerOne platform have identified 72,000 vulnerabilities.
As the company’s community matures, so does the quality of the incoming reports from cybersecurity researchers. In 2015, 68 percent of the cybersecurity reports in public programs either had clear or nominal benefits for the organizations launching the programs. In 2017, that number had climbed to 74 percent.
Mickos is upbeat that HackerOne will become more effective at identifying vulnerabilities as it experiments with pooling the resources of elite hackers. At Black Hat, the company is launching a live cybersecurity event with 100 of its most elite hackers flown in from across the world. “They are collaborating with each other, competing against each other,” Mickos said. In the future, the firm plans to build on this experiment, drawing gamification lessons from the world of eSports to magnify the talents of hackers. “We are already good, but we could be better,” Mickos said.
About the Author(s)
You May Also Like



.png?width=300&auto=webp&quality=80&disable=upscale)


.png?width=300&auto=webp&quality=80&disable=upscale)