Smart dust could multiply IoT’s security problem.
December 7, 2016

By Thomas Pore
Here are two eye-opening facts: There are millions of compromised devices on the internet and, bots generate a significant amount of web traffic. Malicious bots can take our personal information, host web sites selling contraband, and participate in massive DDoS attacks. Who knows what else they could do in the near future. As an Internet society, we have thus far failed curtail this growing problem. Vendors today are still shipping IoT devices that are easy to compromise. Some products are even infected with malware before they leave the manufacturing facility. As concerning as it may already be, this issue could be about to explode exponentially.
Explosion of IoT Devices
The explosion of infected devices is likely to come in the form of the Internet of Things (IoT).
Gartner Inc. forecasts that 6.4 billion connected things would be in use worldwide in 2016, up 30 percent from 2015, and will reach 20.8 billion by 2020. In 2016, 5.5 million new things will get connected each day.
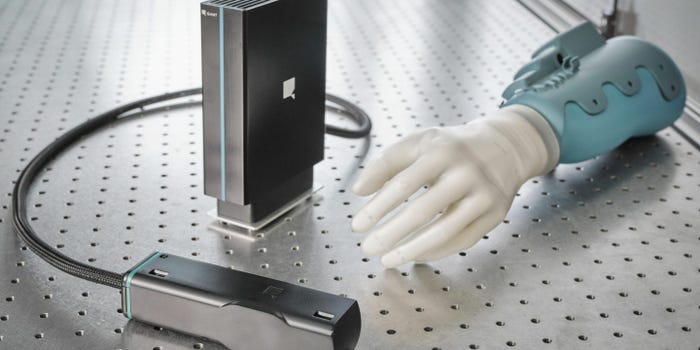
IoT devices can come in the form of tiny microscopic sensors, a few millimeters in size, known as smart dust. These ultra-low-power low-bandwidth devices are able to send sensory data such as temperature, vibration, GPS coordinates, and more back to an Internet host for further analysis. Smart dust could prove useful for tracking packages and for providing shippers and receivers with location information during transit. These sensors could be stuck on airline luggage to provide accountability to baggage handlers that would help alleviate a traveler’s concerns over lost luggage. It could even be used for tracking the location of a person… just toss some smart dust on them during a distracted moment and you’ll know their exact location at any time when they wear that jacket.
The IoT Security Concern
But smart dust could have a shadow side. Autonomous vehicles, the connected home, the smart building, are all projects designed to automate and ease daily tasks or provide optimized energy consumption. As more of these IoT devices come online, it is uncertain who will maintain the security of these devices. As infection technologies advance, who will maintain existing IoT platform deployments? Who will provide security patches? Will patches be provided automatically? If a smart home is tricked out with more than 200 sensors and sold to another party, will user accounts and “smart home training” be included as part of the closing? Don’t count on it.
Related: What’s in Store for IoT Security in 2017
The challenge associated with technologies such as smart dust is how to handle the disposability of these devices. They could run for years with the latest rechargeable battery technologies. Once their initial task is completed, they could end up in a landfill, still connected, and capable of communicating to the internet via 6LoWPAN. Although the traffic generated by an individual smart particle is extremely small, if smart dust use explodes and these discarded specs of IoT dust get compromised, large-scale disruptions could have long-lasting impacts against targeted victims. Even if available bandwidth is limited, there is power in numbers! Our Internet community needs to consider who owns the responsibilities of an IoT device once it’s been discarded. How do we clean up a mess like this?
Where We Are Today
We know that devices currently sitting on store shelves or deployed in homes are vulnerable. We know for example that a Wi-Fi refrigerator has been compromised and has been used to spam tens of thousands of email accounts. We know that internet-facing DVRs are one type of IoT device that poses an immediate risk of compromised to become an army of weapons used in DDoS attacks. Currently, millions of devices have shipped with default credentials, putting the security responsibility on the unknowing end user.
We have learned that consumers buy products that improve their way of life. Unfortunately, manufacturers are known to compromise on details such as security in order to be first-to-market. Today, it seems the general public isn’t concerned about the lack of security so long that they are not directly affected and Netflix/YouTube streams flawlessly.
What We Can Do
We need to make sure that Smart Dust has a hard-coded end of life where it simply stops working through a self-destruction mechanism triggered when the initial intended use has ended. BCP 38 can be implemented to prevent source address spoofing and legislation could be considered to enforce IoT guidelines. The FCC has already established a certification process on all devices that emit or receive radio-frequency spectrum as a means to verify that they don’t interfere with radio communication. A letter from FCC Chairman Tom Wheeler outlined that a plan was underway to address the cyber risks associated to IoT devices. Unfortunately, the timing of this letter is not ideal as future actions on this matter have been suspended with the change in administrations. It is yet to be seen if the Trump administration will pick up the ball and addresses the IoT cybersecurity issue. If not, the issue of DDoS will continue to grow.
Thomas Pore is an expert in network behavior and cyber threat intelligence analysis. He is a regularly quoted as a cyber security resource for global media outlets and is an adjunct professor teaching ethical hacking. Pore is currently director of IT and field engineering at Plixer. His responsibilities include establishing, planning, and implementing the company’s IT and security policies and procedures, leading the company’s professional services team and driving product features and roadmap. He established, and is responsible for, the Malware Incident Response and Advanced NetFlow Training programs offered throughout the United States. Pore regularly travels the world meeting with customers, helping them optimize threat detection strategies and incident response solutions.
You May Also Like

.png?width=700&auto=webp&quality=80&disable=upscale)
.png?width=300&auto=webp&quality=80&disable=upscale)


.png?width=300&auto=webp&quality=80&disable=upscale)